
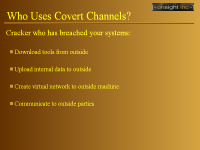
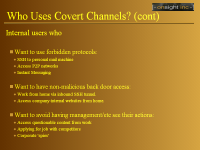





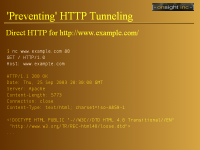

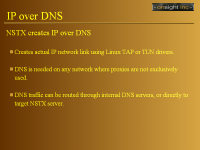




Users, hackers, and crackers alike can use many means to stealthily connect through firewalls and proxies to avoid detection. In this session Bri Hatch will show a variety of methods of creating covert channels, from standard encryption protocols such as SSH to abhorrent protocol abuses such as TCP over DNS.
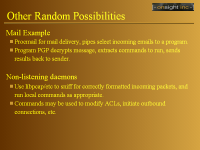
There is no way to cover all the different possibilities for covert channels that are out there, much less each tool that could be used to create one. This talk hoped to introduce enough diverse methods to get attendies thinking like paranoid administrators, while acknowledging that many of them will come away with new uses for these kind tricks themselves.
Due to the use of images in several of the slides, I wasn't able to get the images for the web smaller than 800x600, so I apologize for that. It was that, or have the text flowing off on a number of pages.
As always, if you have need of a good Linux security guy, drop me a line.