![]()
Presentations available online
Below are recent presentations I've given, in reverse cronological order. If you're interested in having me present at your organization/function/etc, just drop me a line.
Video on LFNW's YouTube channel - Obfuscation Games. Sad that we can't hear the audience though, because they were a hoot and absolutely critical to the talk!
Video on LFNW's YouTube channel - Python Unit Testing. (Audio and video aren't in sync, perhaps put a sticky note over me gesticulating.)
Video on SeaGl's site on YouTube SeaGL 2023 day 2 track 4.
So I sat down and went through Gopika's slides! I couldn't see the 'next slide' display, so I could only see the presentation as it came up for everyone. It was a hoot, and more exhausting than I'd have anticipated.
Shout out to Gopkia Subramanian who made a presentation with such a natural flow I was able to do a passable job. You can see her pre-recorded version (which found the next day!) on the SeaGL Live Stream Recording
And for those who want to see the "we're doing it live" version, it's on SeaGL 2023 day 1 track 2 . Sorry for the naughty word as I realized the talk was twice as long as I expected. It's a shame you can't see the face of people who came in late as we all asked "are you the presenter?" while the presentation was already underway. I relied on room involvement, notably Jay Houppermans - thanks for being there and providing corrections and more colour commentary!
In this talk I show how to create custom command line tab complete for easy things like boolean arguments (e.g. -d or --no-frobnicate), or more complex things like auto completing usernames (e.g. --reporter username) to save you time and decrease errors. Here's the original description:
Tab completion saves time typing keys, and helps you remember those --long-esoteric-options without pulling up a man page. You can create bash completions for your custom tools as well, which can help your coworkers and yourself down the road. We’ll build up simple and advanced bash tab completions so you can build your own and save time!The trimmed video is not up yet, but you can watch from the Day 2 Track 1 livestream at 5:59:10 via youtube for now.
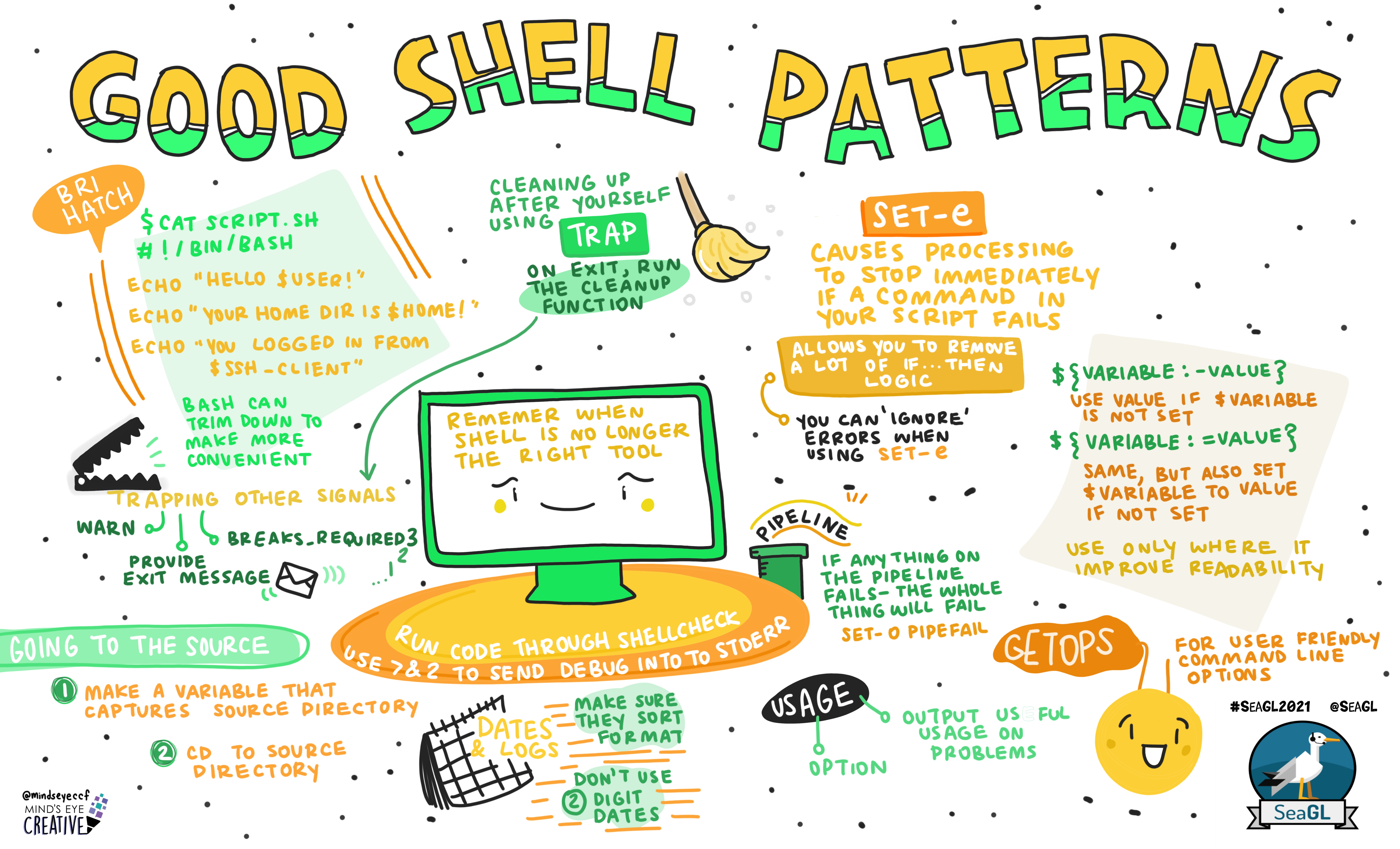
We'll discuss tried-and-true code snippets you can use to make your code more reliable, easier to read, and quicker to debug. Enjoy the elegance of "cd $(dirname $0)", performing actions only on successful exit, and informational help messages. We'll cover all those minor changes that continually come up in our code review sessions that reap outsized rewards.The video is available on the SeaGL Archive, hosted with the good folks at archive.org (Direct archive.org video link)
Lastly, SeaGL engaged Mind's Eye Creative to produce this graphical slide of the talk as well!
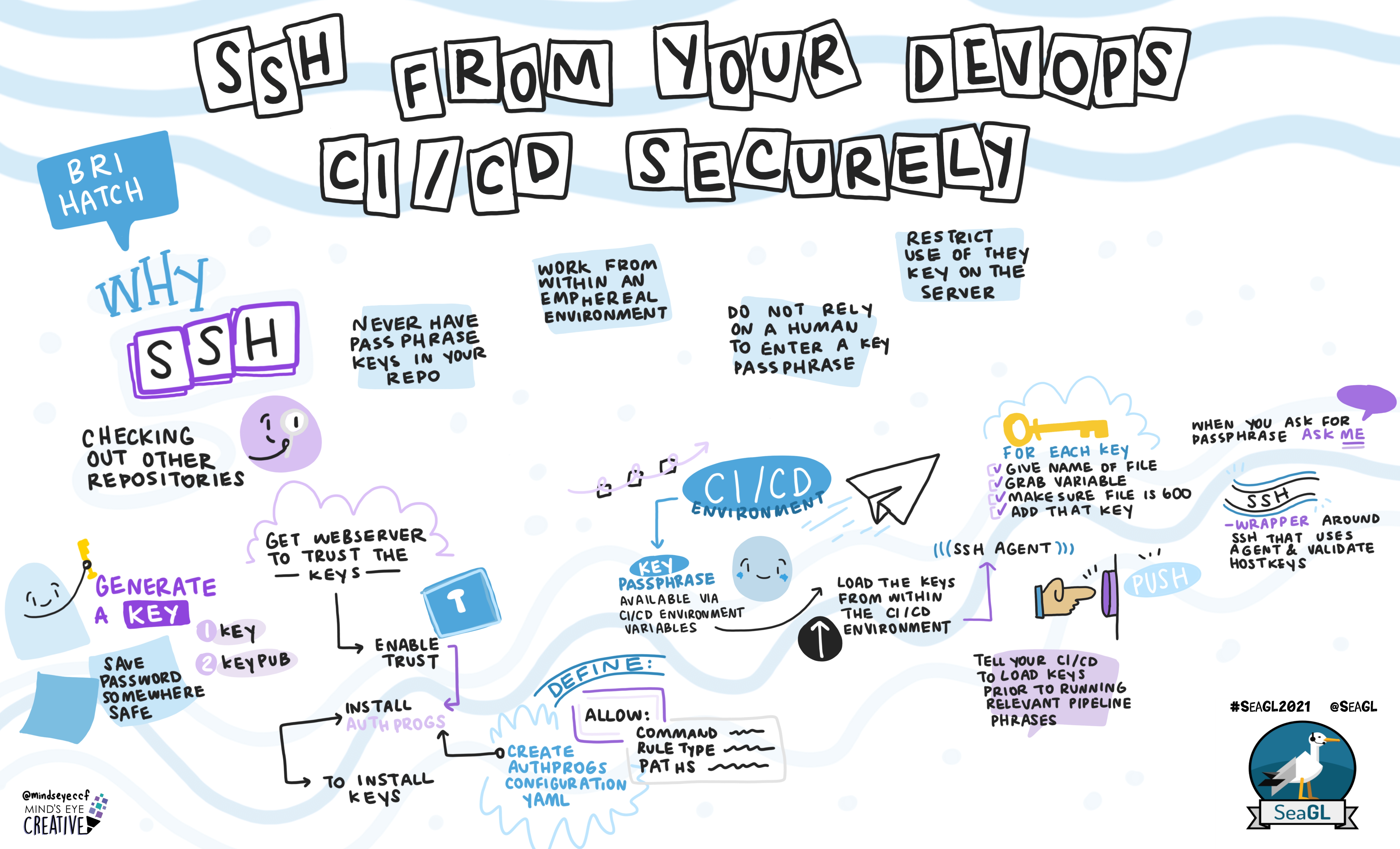
Your CI/CD pipeline needs to make things happen, and often that means hitting other machines via SSH or rsync. Since no human is at the keyboard to type a password, how do you automate this securely? We'll show alternatives to passwordless keys in your repository (BAD!!!), describe the security implications, and how you can assure that these keys are usable only for the commands they require.Video available on the Seagl Archive, (Direct archive.org video link)
Sometimes you need to write software to solve problems and
automate systems. But sometimes all you really need is a
good editor and a few tricks up your sleeves. I find myself
frequently turning to vim to handle repetitive tasks, and
create commands I'll run from the command line. Why write
python when some efficient macros will do, or an occasional
:%s will save you time? And naturally that godsend for fixing
typos, xp.
Once SeaGL is done processing the video I'll link to it.
No prior knowledge of HTTP or networking is required, but even those comfortable writing web requests at the command line will learn a thing or two.
This is a highly condensed version of the LFNW
No prior knowledge of HTTP or networking is required, but even those comfortable writing web requests at the command line will learn a thing or two.
Video is available on youtube as part of the full day streaming. (Starts at 4:49:54)
- Task automation with Python and DoJobber, LFNW 2018
-
DoJobber allows you
to execute large complex and interwoven tasks by breaking them into
individual components and defining any interdependencies. DoJobber
determines the right order to run tasks and will try every unblocked
task until it encounters a failure. This means it is completely
idempontent - you can run it repeatedly until it succeeds.
Rather than a yaml-based syntax with many plugins, DoJobber lets you write in native python, so anything you can code you can plumb into the DoJobber framework. DoJobber is conceptually based on a Google program that was used for automating service and datacenter spinups.
The presentation video is available on YouTube.
- Serving Secrets Securely, SeaGL 2016
- How do you securely provide sensitive information to automated systems without typing in passphrases at 2 in the morning? Bri will discuss the ways he allows headless daemons to access secrets with minimum security impact. Topics will include ssh and gpg agents, encfs partitions, full disk encryption (including remote unlock), hashicorp vault, SSSP - the simple socket secret provider (Open Sourcing shortly!) and others.
- Production Trenches: Pitfalls and Pratfalls (or how I learned to stop scheduling downtime and love the SLA) - LFNW 2016
-
Whether your title is Production Engineering, DevOps, SRE, or IT doesn't matter. You're the lifeblood of the company, the team that invisibly makes everything work. You, my friend, carry the pager.
In this talk, I passed on wisdom, wit, and embarrassing stories, replacing my normal code-filled presentations with humour and humiliation. You'll learn how to run a solid yet nimble production infrastructure, organize your workload, avoid burnout, and automate caffeine ingestion.
You may you end up making the same mistakes I made, but at least you'll make them your own.
This talk was recorded at LFNW this year, and is available on YouTube. The LFNW site page is at http://lfnw.org/node/3898, and you can submit feedback there if you attended.
- Production Trenches: Pitfalls and Pratfalls (or how I learned to stop scheduling downtime and love the SLA) - SeaGL 2015
-
The precursor to the same talk at LFNW 2016.
Suggest you look at the LFNW version above instead, as many of the verbal bits have been captured in slides, and some bugfixes in the logging output.
- Git Administration, Hooks, and Dangerous Things (SeaGL 2014)
- Managing your git repositories with gitolite-admin. We'll go in depth about different access levels, grouping users, and allowing selective users to change repo history. We'll discuss how you can use server-side git hooks to enforce policy, send commit messages, or even trigger actions such as pushing content to production. We'll use a DNS server config as an example, where all management is in git and no changes are made directly on the DNS servers any more.
- Python For Converts (SeaGL 2014)
- Python is a powerful scripting language that can be used for anything between short few-liners, cron jobs, to full web applications. It's not the language of the week, but it's also not the language of perpetual rewrites.
As a long time Perl advocate and now Python convert, I show you what you need to learn to start being proficient in python. This class will discuss the idioms that make python unique, introduce you to the "No, there's really only one way to do it" mindset, and get you past the disdain for forced indentation.
Note that the slides without the talk itself, are somewhat low on discussion, YMMV.
- Python For Converts (LFNW 2014)
- Same as the SeaGL talk, but with unfixed bugs.
- SSH Login Automation, Tunneling, Authprogs, and More
- SSH replaced insecure protocols like telnet and ftp ages ago, but it has far more power than simple remote login capabilities. In this talk we'll cover passwordless SSH w/ pubkeys and ssh-agent, locking down access with authorized_keys options, port forwards and SOCKS proxies, ssh 'bouncing', and more.
Also demonstrates Authprogs, an SSH remote command authenticator, which allows you to restrict which commands can be run, thus limiting what access a trusted key is granted.
- SSH Login Automation, Tunneling, Authprogs, and More
- I'm presenting this at SeaGL 2013. Looking forward to
this new Linux/Open Source conference. See http://seagl.org for more information.
- Linux Fest Northwest Talks
- I have two talks at Linux Fest Northwest this
year, Network
Protocols Illuminated and Shell
Scripting from Scratch. After a long stretch of minimal speaking
engagements (limiting myself to the occasional GSLUG lightening talk)
it was a pleasure to be back at LFNW and see throngs of Linux veterans
and new folk alike.
- The Command line is for Everyone
- An attempt to dispell the "only uber-hax0rs can understand the command line" myth, this talk from Linux Fest Northwest shows how the command line works - arguments, redirection, etc - to remove
the mystery and lead you down the trail to real power. Muahahaha.
- Linux Security Overview, Redux
- I recycled my talk from ISSA for TacLUG,
condensing the 2.25 hour talk into about 1 hour. Many slides were summarized,
skipped, or at least overlooked.
- Practical SSH Encryption, Tunneling, and Automation
- A 1 hour presentation I gave at LinuxFest Northwest
this year. I don't think I should have called it 'practical' because really it
covers more of the essoteric and bizzare hackish things you can (and should)
do with SSH.
- Perl Security Overview
- A 2 hour presentation (written in the same amount of time) I
gave at the November Seattle Perl
Users Group. Overview of common problems and pitfalls when
developing in Perl.
- File Integrity Checking with AIDE
- Jeremy Reed and I tag-teamed this talk. My sections are available here.
- GnuPG/PGP Encryption
- A 1 hour presentation at
GSLUG
overviewing how PGP works, how to create, exchange, and verify keys, and
how to sign and/or encrypt files.
- Covert Channels
- A 1 hour presentation at
SecureWorld Expo
discussing various nefarious ways to communicate covertly, from steganography,
SSH and SSL forwarding, to application tunneling such as TCP over HTTP or IP over DNS.
- Crypto Tunnels with SSH and SSL
- A 1 hour presentation at GSLUG
(Greater Seattle Linux User Group) covering how to use SSH tunneling
(LocalForward / RemoteForward) and SSL tunneling (using Stunnel) to protect
your cleartext protocols.
- Linux Security Overview
- A 2 hour presentation at ISSA Puget Sound in July, 2003. Covers Bastille Linux (basic), identifiying and locking down services manually (intermediate) and the kernel-level security (advanced) with traditional root, capabilities, LIDS, and Systrace.
- VPNs and Crypto Tunnels
- A talk about various VPN technologies and cryptographic Tunnels available on Linux, presented at Real World Linux in April 2003.
- Linux: The secureable operating system -- AKA, 'every linux security hook in 60 minutes or less'
- This was a insanely ambitious attempt to cover all linux kernel
security in one hour that I presented at LinuxFest Northwest.
I only made it through 98 of the 130 slides.
![]()